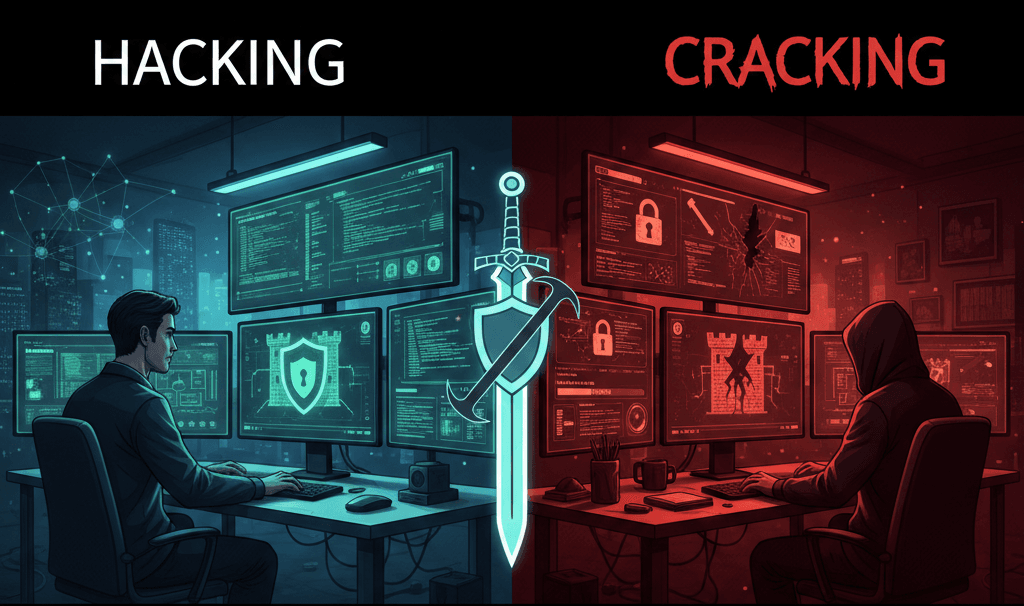
In the world of cybersecurity, “hacking” and “cracking” are often used interchangeably by the general public, but they carry very different meanings within the tech community. The core difference lies in intent and permission.
What is Hacking?
Originally, “hacking” referred to someone who was highly skilled at programming and enjoyed pushing computer systems beyond their designed limits. Today, it is a neutral term that describes the act of exploring and modifying a system.
- The Intent: Often educational or protective. Many hackers (known as White Hats) are hired by companies to find security holes so they can be fixed.
- The Skillset: Deep knowledge of networking, operating systems, and programming.
- Analogy: A professional locksmith who tests a bank’s vault to see if it’s truly secure.
Hacking is a broad field, and it’s usually categorized in two ways: by the “Hat” (the intent of the person) and by the Method (the technical way the hack is performed).

Types of Hacking by Intent
In the cybersecurity community, hackers are often categorized by “hat colors” to describe their ethics and legal standing.
- White Hat (Ethical Hacker): These are the “good guys“. They have permission to break into systems to find vulnerabilities so they can be fixed. They are often employed as security consultants or “Penetration Testers“.
- Black Hat Hacker (Cracker): These are the “bad guys” we discussed earlier. They hack for personal gain, money, or to cause damage. Their activities are illegal.
- Gray Hat: These hackers fall in the middle. They might break into a system without permission (illegal) but without malicious intent. For example, they might find a bug and then email the company to offer to fix it for a fee.
- Red Hat (The Vigilantes): These hackers specifically target Black Hats. Instead of reporting them to the police, they often launch aggressive counter-attacks to destroy the Black Hat’s computer or network.
- Blue Hat: Historically, these are outside security professionals invited by companies (like Microsoft) to bug-test software before it launches.
- Green Hat (The Newbies): These are beginners who are eager to learn. They often ask a lot of questions in forums and experiment with tools they find online.
Types of Hacking by Method
This describes what is being targeted or the specific technique being used.
Common Targets
- Network Hacking: Intercepting data as it travels across a network (like stealing info from public Wi-Fi).
- Website/Web App Hacking: Exploiting vulnerabilities in a website’s code to steal user data or change the site’s appearance (defacement).
- Email Hacking: Gaining unauthorized access to an email account to send spam, steal identity, or read private messages.
Common Techniques
- Phishing: Sending fake emails that look real (like from a bank) to trick you into typing your password on a fake login page.
- Social Engineering: Manipulating people into giving up secret information. This is “hacking the human” rather than the machine.
- DDoS (Distributed Denial of Service): Flooding a website with so much “fake” traffic that it crashes and becomes unavailable to real users.
- SQL Injection: Inserting malicious code into a website’s entry fields (like a search bar) to trick the database into revealing hidden information.
What is Cracking?
Cracking is essentially “hacking with a crowbar“. It is the act of breaking into a system, network, or software with malicious intent or for personal gain. If someone is stealing data or breaking software to use it for free, they are “cracking“.
- The Intent: Malicious. This includes stealing sensitive data, spreading malware, or bypassing software licensing (e.g., “cracked” versions of games).
- The Skillset: While some crackers are highly skilled, many use pre-made scripts or tools (often called Script Kiddies).
- Analogy: A thief who picks a lock to steal what is inside the vault.
Common Types of Cracking
- Password Cracking: Using brute-force or dictionary attacks to guess user passwords.
- Software Cracking: Modifying a program’s code to remove copy protection or registration requirements (e.g., using a “Keygen“).
- Network Cracking: Breaking into a secured Wi-Fi or local area network (LAN) to intercept traffic.
The “Hackers Build, Crackers Break” Rule: In the tech community, hackers view themselves as “builders” who enjoy the complexity of systems, whereas crackers are seen as “breakers” who only care about the shortcut to a result.