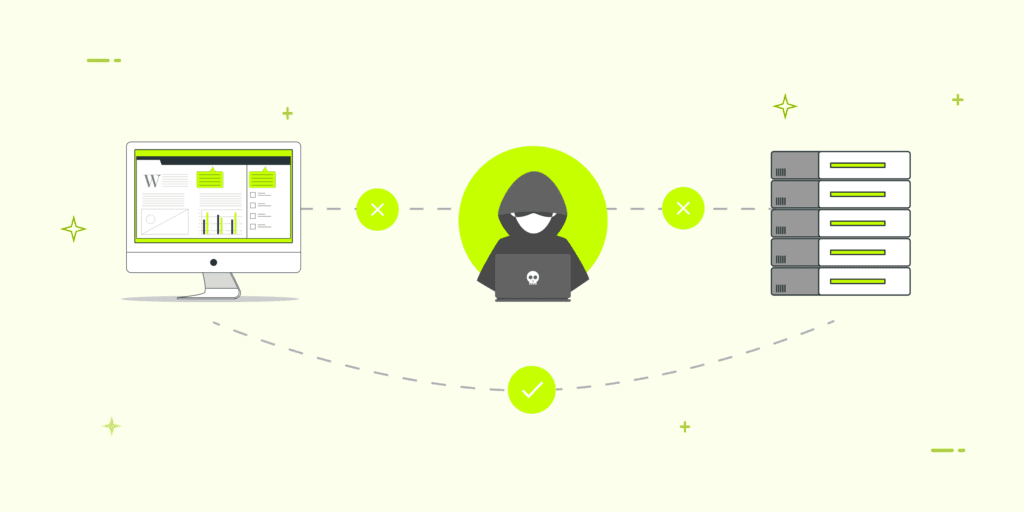
A Man-in-the-Middle (MitM) attack is a type of cyberattack. In this an attacker secretly inserts themselves between two parties who are communicating, intercepting and often altering the data being exchanged without either party knowing.
The attacker effectively becomes the “Man in the Middle. He relays the messages between the two victims while maintaining the illusion of a normal, private connection.
How an MitM Attack Works?
An MitM attack generally involves two main phases: Interception and Decryption/Manipulation.
- Interception: Attacker must first compromise the communication channel to insert himself into the data-stream. Common interception methods include:
- Rogue Wi-Fi Access Points: The attacker sets up a fake, unsecured Wi-Fi hotspot (an “Evil Twin“) in a public place (like a coffee shop or airport) with a trusted-sounding name. When a victim connects, all their traffic is routed through the attacker’s device.
- ARP Spoofing: On a local network, the attacker sends fraudulent Address Resolution Protocol (ARP) messages to associate their MAC address with the IP address of the default gateway (router). This tricks the victim’s device into sending all its traffic to the attacker’s machine instead of the router.
- DNS Spoofing/Poisoning: The attacker manipulates a Domain Name System (DNS) server to redirect a user trying to visit a legitimate website (like a bank) to a fake, malicious website controlled by the attacker.
- Decryption and Manipulation: Once the data is intercepted, the attacker’s job is to read and potentially modify it. Since most modern communications use encryption (like HTTPS/TLS), the attacker employs methods to break or bypass this security:
- SSL/TLS Stripping: This technique downgrades a secure HTTPS connection to an unsecure HTTP connection. When the user tries to access a secure site, the attacker intercepts the request, communicates with the real server securely, but sends an unencrypted version of the website to the user. The user sees no padlock and no “https,” allowing the attacker to read all data sent in plaintext.
- Session Hijacking: The attacker steals the user’s session cookies (which contain authentication information) after the user has logged in. The attacker can then use the cookie to impersonate the legitimate user and access the account without needing their password.
Prevention Measures
The best defenses against MitM attacks rely on encrypting data and verifying communication endpoints:
- Always Use HTTPS: Look for the padlock icon and ensure the URL begins with https://. This indicates that the connection uses TLS/SSL encryption, making it much harder for an attacker to decrypt intercepted data.
- Avoid Public Wi-Fi for Sensitive Transactions: Do not access financial or highly confidential accounts on unsecured public Wi-Fi networks.

- Use VPN: Virtual Private Network (VPN) encrypts all of your internet traffic from your device to the VPN server. This creates a secure tunnel that shields your data from local network attackers.
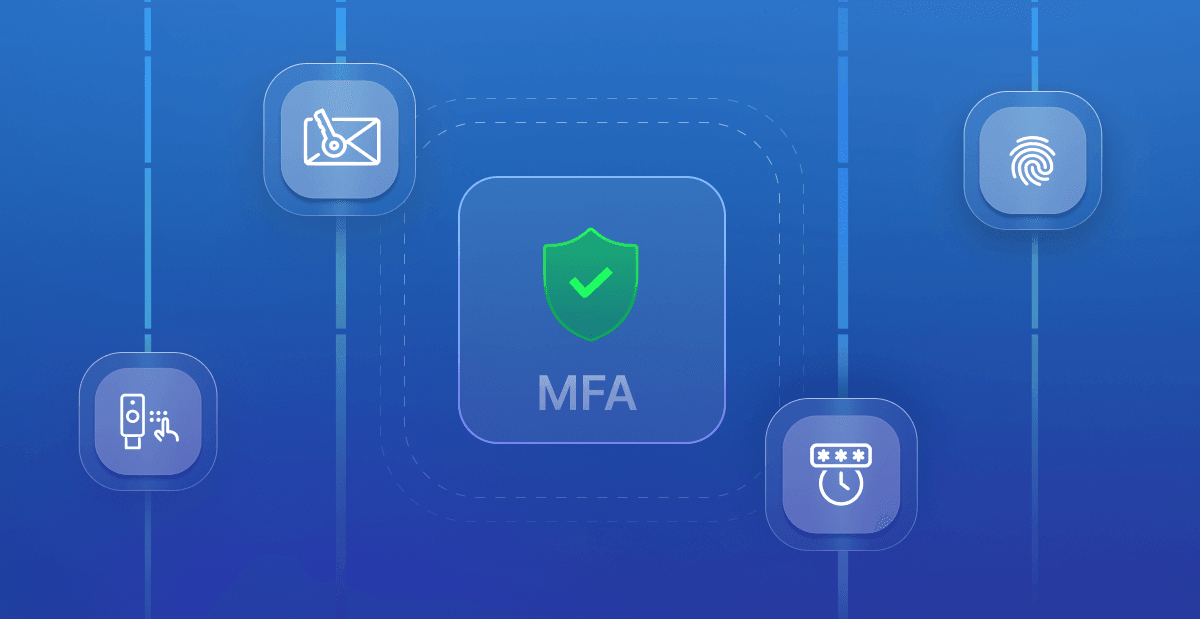
- Enable Multi-Factor Authentication (MFA): Even if an attacker steals your login credentials via an MitM attack, MFA prevents them from logging in without the second factor (like a code from your phone).
- Keep Software Updated: Regularly update your operating system and web browser to ensure you have the latest security patches. These security patches provide protection against known vulnerabilities.
Would you like to know more about the difference between HTTP and HTTPS?