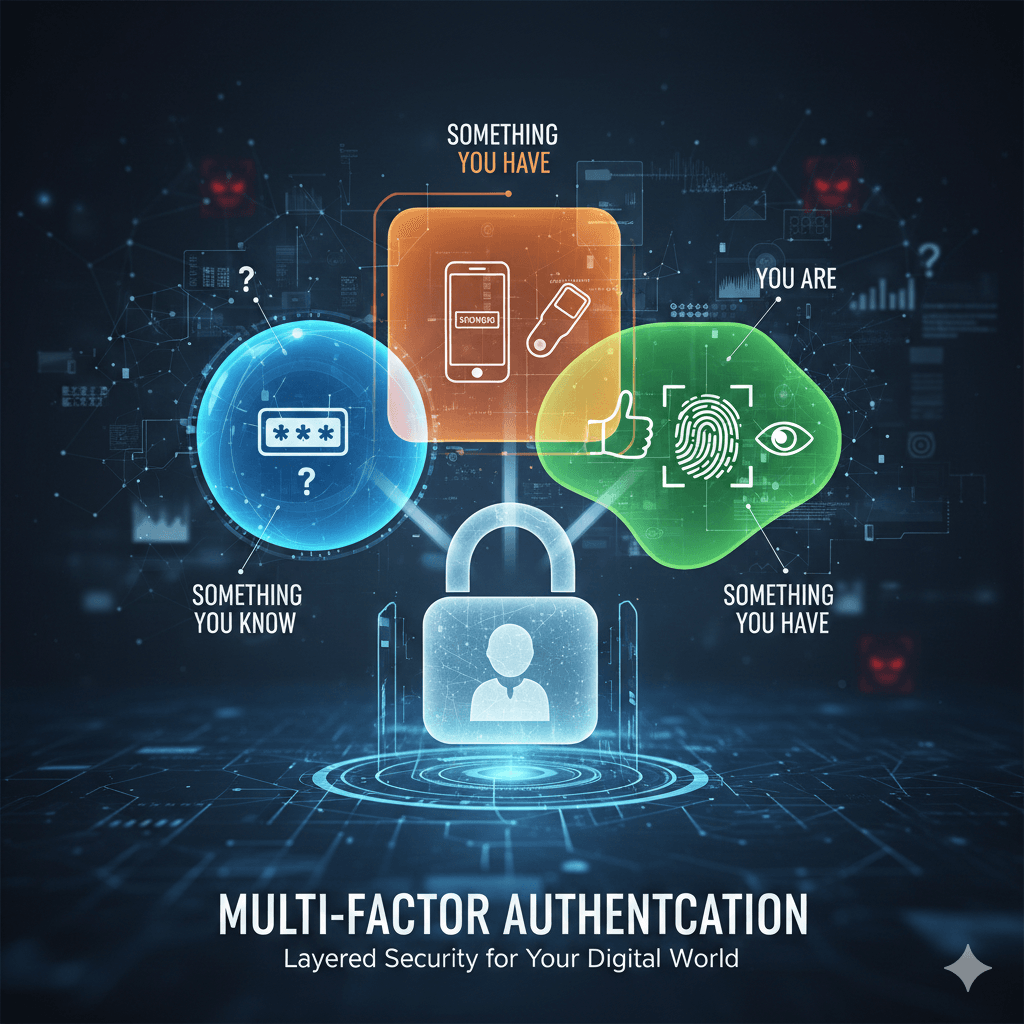
Think of Multi-Factor Authentication (MFA) as a high-security lock that requires more than just a single key to open. It’s a security system that verifies a user’s identity by requiring two or more separate forms of evidence (factors) before granting access to an account.
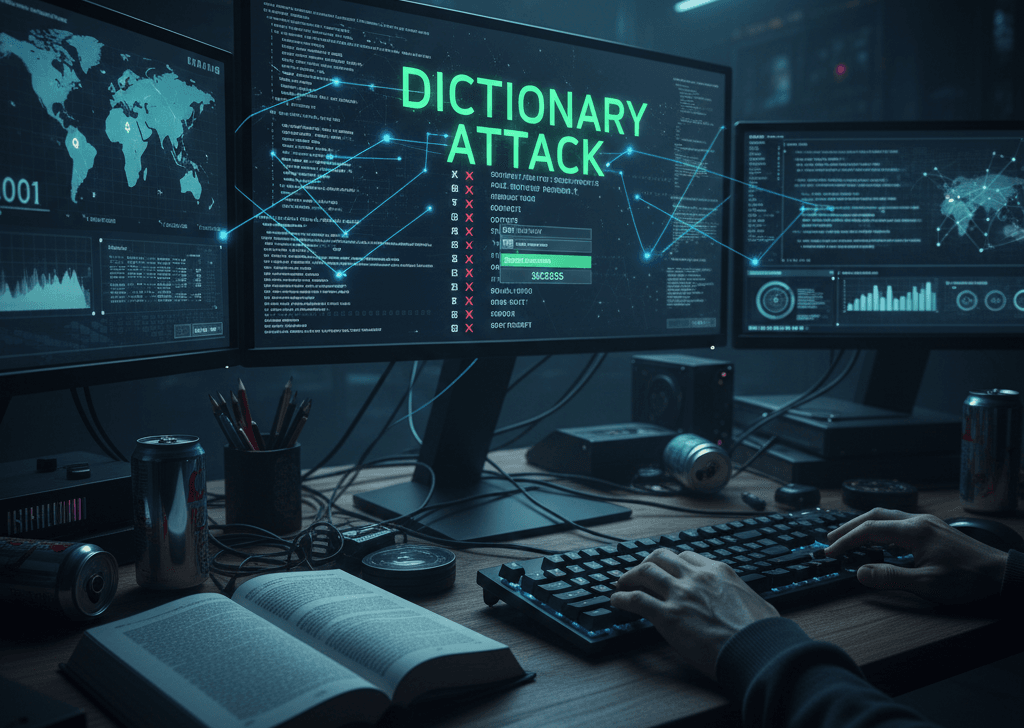
In the old days, a password was enough. Today, because passwords are easily stolen or guessed, MFA adds extra layers of defense to ensure that even if someone has your password, they still can’t get into your account.
The Three Core Factors
Security experts generally group MFA requirements into three distinct categories. To be true MFA, the system must use factors from at least two of these different groups:
- Something You Know (Knowledge): This is the most common factor. It involves information that only the user should have memorized. Examples: Passwords, PINs, or answers to “secret” security questions.
- Something You Have (Possession): This involves a physical object or a digital token that you own. Examples: A smartphone (receiving a text code), a physical security key (like a YubiKey), or a software-based authenticator app (like Google Authenticator).
- Something You Are (Inherence): This is based on biological traits, often referred to as biometrics. Examples: Fingerprint scans, facial recognition (FaceID), or iris patterns.
Why is Multi-factor Authentication So Important?
The goal is simple wiz. Layered Defense. If one factor is compromised, the others still stand in the way.
- Prevents 99% of Bulk Attacks: Even if a hacker buys a list of leaked passwords on the dark web, they won’t have your physical phone or your thumbprint.
- Reduces Identity Theft: It makes it significantly harder for attackers to impersonate you to gain access to bank accounts or corporate data.
- Compliance: Many industries (like finance and healthcare) now require MFA by law to protect sensitive information.
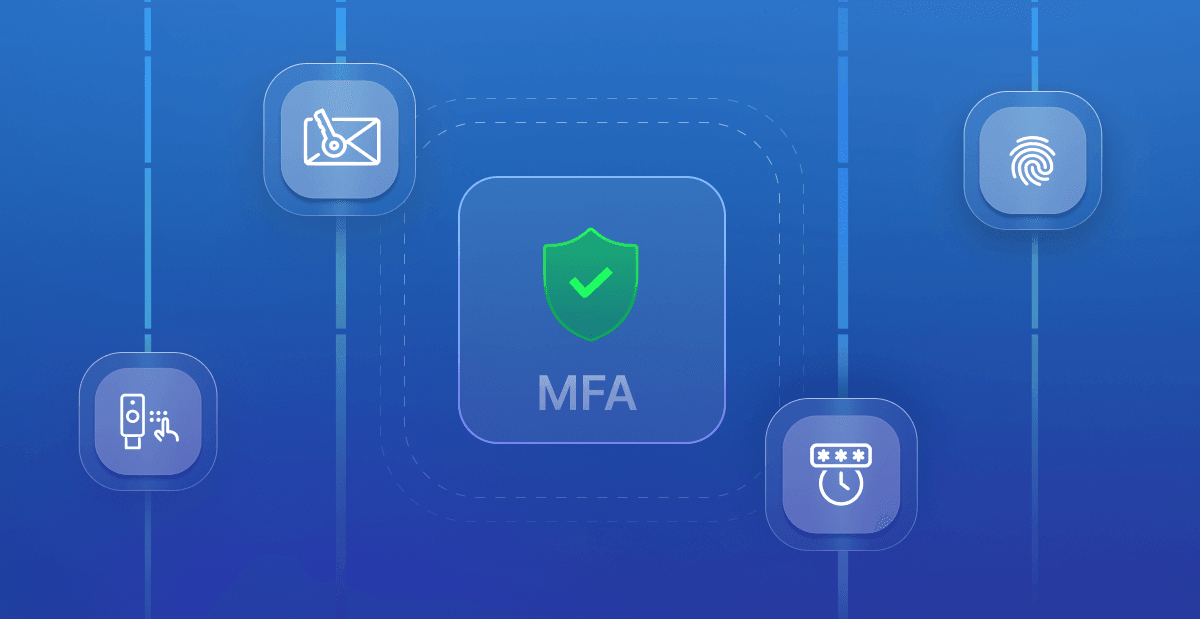
Common MFA Methods
While all MFA is better than none, some methods are more secure than others:
- SMS/Text Codes
- Authenticator Apps
- Biometrics
- Physical Security Keys

SMS-based MFA is widely used but is technically the weakest form of MFA because hackers can sometimes perform a SIM swap to intercept your text messages.