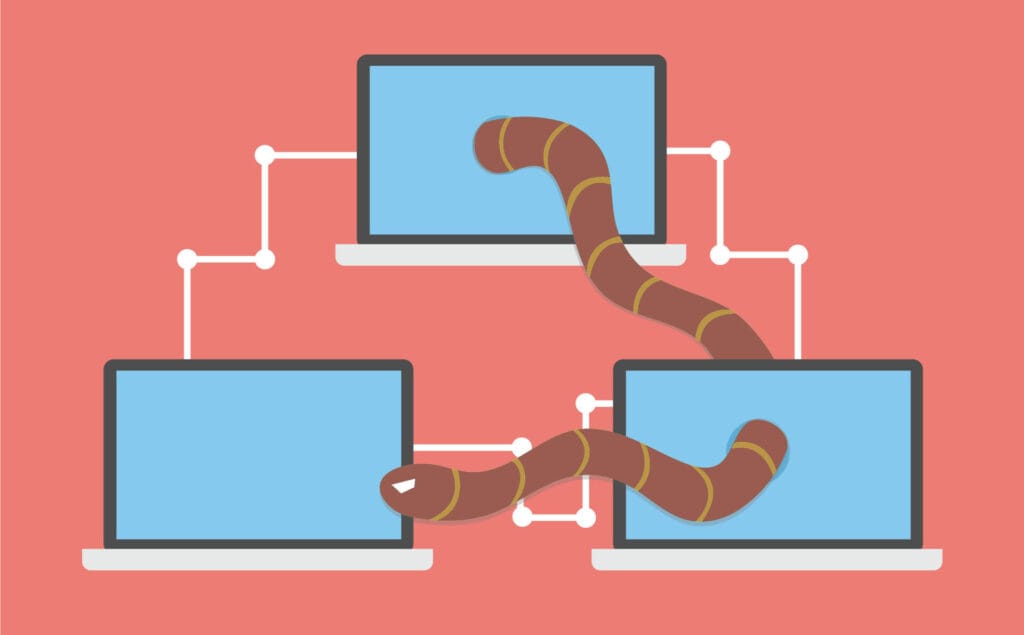
A computer worm is a standalone malicious program that copies itself and propagates across computer networks without needing to attach itself to an existing file or program (unlike a traditional virus) and without any human intervention to spread.
The primary characteristic that defines a computer worm is its ability to self-propagate. Once it breaches a system, it scans the network for other vulnerable systems and automatically sends copies of itself to infect them.
How Computer Worm Spread?
Worms are incredibly fast and dangerous because they don’t rely on the user to click or execute a file to spread. They exploit security weaknesses and network connections:
Exploiting Vulnerabilities
The most common method is by targeting unpatched flaws in operating systems or software applications. The computer worm exploits the vulnerability to install itself.
Network Protocols
Once installed, it uses the host computer’s network connection to scan the local network (LAN) or the internet for other machines with the same vulnerability.
Self-Replication
It replicates itself and transmits its copies to the newly discovered vulnerable machines.
Common Vectors
- Email: Mass-mailing worms access the user’s contact list and send copies of themselves as attachments or links.
- Instant Messaging: Spreading through chat applications using malicious links.
- Removable Media: Copying itself onto USB drives, which then carry the worm to other connected computers.
- File Sharing: Disguising itself as legitimate files on peer-to-peer (P2P) networks.
The Danger of Worms
Because they can spread automatically and rapidly across networks, worms can cause large-scale and immediate disruption. Their impact can include:
- Network Overload: The continuous self-replication and transmission consume massive network bandwidth, causing the network and internet to slow down or crash completely (a denial-of-service effect).
- Malicious Payload: While some worms just spread, many carry a “payload” that performs a malicious act, such as:
- Installing backdoors for remote hacker access.
- Stealing sensitive data.
- Encrypting files (like the famous WannaCry worm, which was a ransomware worm).
- Launching distributed denial of service or DDoS attacks.

How to Defend Against Worms?
The defense against worms is focused on patching vulnerabilities and monitoring network activity:
- Apply Security Patches: This is the most critical defense. Always keep your operating system (OS), applications, and security software fully updated to close the vulnerabilities that worms exploit.
- Use a Firewall: A firewall can block unauthorized incoming and outgoing network traffic, preventing the worm from both entering your system and spreading to others.
- Install and Update Antivirus/Anti-Malware: Use a comprehensive security suite that scans in real-time and detects the presence of worm code.
- Be Cautious of Emails/Links: Although worms don’t require a click, many still use social engineering (like email attachments) to gain initial entry. Never open unexpected attachments or click links from unknown senders.