Cryptojacking is a type of cyberattack. In cryptojacking hacker hijacks computer, smartphone, or server to mine cryptocurrency without your permission. Unlike ransomware, which locks your files and demands money, cryptojacking is a stealth attack. The goal of the hacker is to stay hidden for as long as possible so they can use your device’s processing power and electricity to make money.
How Cryptojacking Works?
There are two primary ways a device becomes “cryptojacked“:
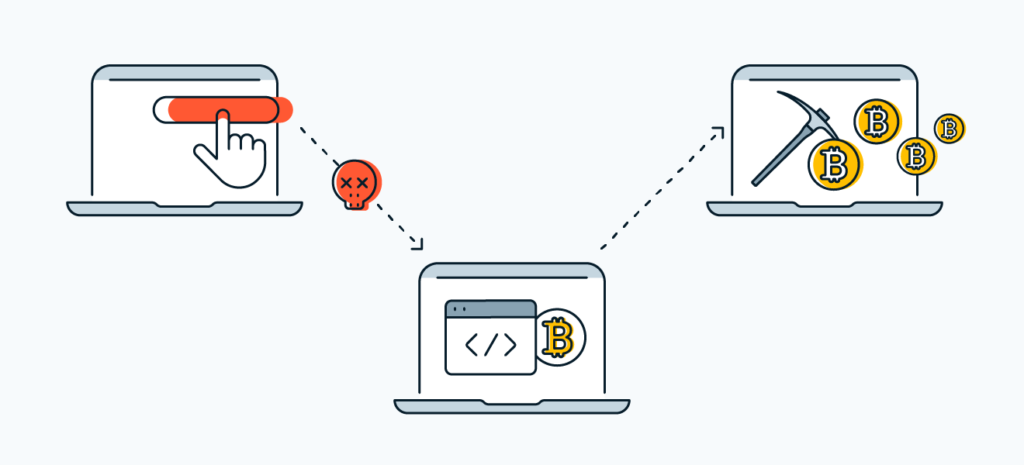
- File-Based Malware: You are tricked into downloading a piece of malware often through a phishing email or an infected software update. Once installed, the mining script runs in the background 24/7, even if your web browser is closed.
- Browser-Based (Drive-By) Mining: The hacker embeds a malicious JavaScript snippet into a website or an online advertisement. When you visit the site, the script automatically executes in your browser. Some “pop-under” windows are designed to hide behind your taskbar or clock, so the mining continues even after you think you’ve closed the browser tab.
Signs of an Infection
Because cryptojacking doesn’t steal your “data,” it steals your “power,” the symptoms are physical and performance-based:
- Device Performance: Your computer becomes sluggish, crashes frequently, or lags during simple tasks.
- Overheating: The device feels unusually hot to the touch, even when you aren’t doing anything intensive.
- The “Jet Engine” Fan: Your computer’s cooling fans start spinning at high speeds and stay loud constantly.
- High Utility Bills: For businesses or cloud-service users, a sudden, unexplained spike in electricity or cloud computing costs is a major red flag.
How to Protect Yourself?
- Use an Ad Blocker: Many ad blockers automatically block known mining scripts.
- Install Anti-Cryptomining Extensions: Browser extensions like NoCoin or MinerBlock are specifically designed to stop browser-based mining.
- Monitor Your Resources: On Windows, use Task Manager (Ctrl+Shift+Esc); on Mac, use Activity Monitor. If you see a process using 80–100% of your CPU while you’re just reading a blog, something is wrong.
- Keep Software Updated: Hackers often use “exploits” in old browsers or operating systems to sneak the mining code onto your machine.