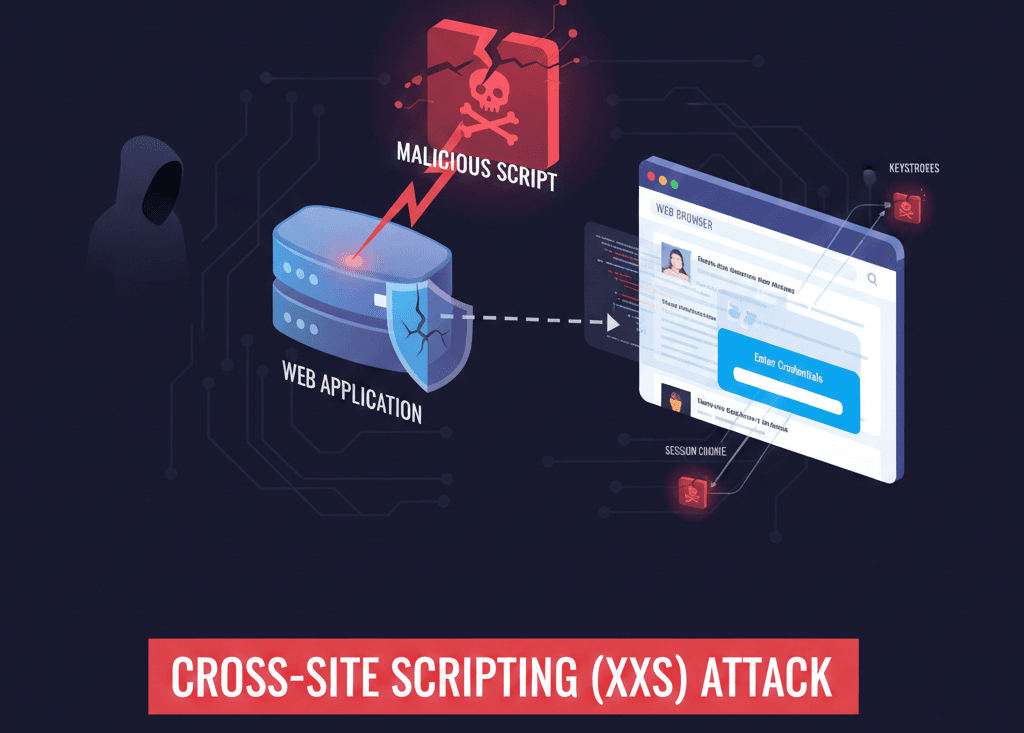
What is Cross-Site Scripting or XSS Attack?
Cross-Site Scripting (XSS) is a type of security vulnerability typically found in web applications. It allows an attacker to inject malicious scripts (usually JavaScript) into web pages viewed by other users. Unlike many other web attacks that target the server directly, XSS targets the users of the website by exploiting…