A Zero-Day Attack is a cyberattack that exploits a software or hardware flaw before the developers are even aware it exists. The term zero-day refers to the fact that the vendor has had zero days to create a patch or fix the issue. These are among the most dangerous threats. The reason is that the standard antivirus software often cannot detect them since there is no signature for the attack yet.
Recent Zero-Day Attacks Faced by Google
Google is a primary target due to the massive user bases of Chrome and Android. In 2025, Google tracked 90 zero-day vulnerabilities exploited in the wild. As of early 2026, security experts have already identified and patched several critical attacks.
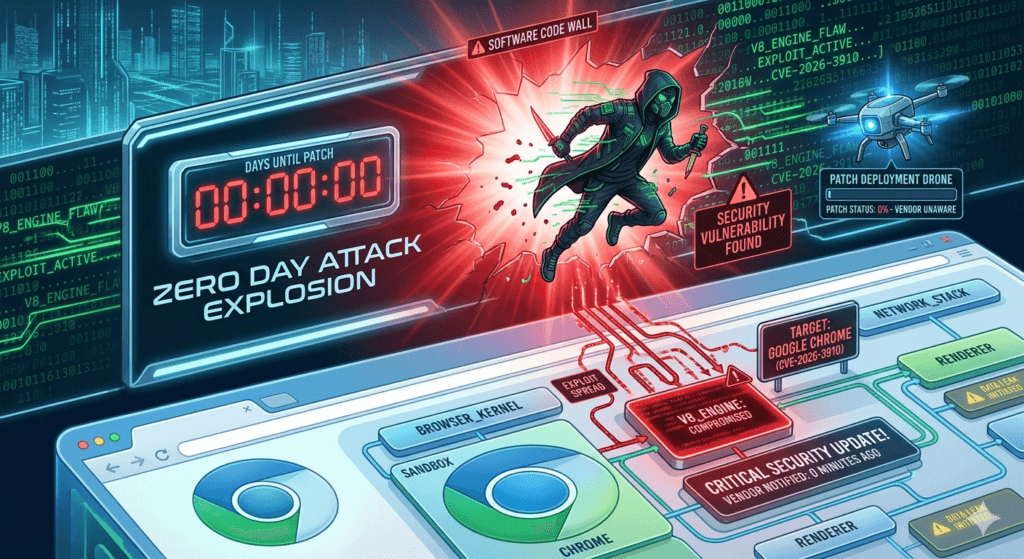
Google Chrome (March 2026)
Just this week (March 16, 2026), Google released an emergency out-of-band update to fix two high-severity zero-days that hackers are exploiting in the wild:
- CVE-2026-3909: A flaw in Skia (Chrome’s 2D graphics library). Attackers could use a malicious webpage to corrupt memory and potentially take control of the browser.
- CVE-2026-3910: An inappropriate implementation in the V8 JavaScript engine. This allowed hackers to execute arbitrary code inside the browser’s sandbox simply by tricking a user into visiting a specific site.
Android & Qualcomm (March 2026)
The March 2026 Android Security Bulletin addressed a record-breaking 129 vulnerabilities, including a high-profile zero-day:
- CVE-2026-21385: This vulnerability affected over 235 Qualcomm chipsets used in millions of Android devices. It was an integer overflow in the graphics component that allowed local attackers to trigger memory corruption. Google confirmed that evidence shows attackers used this vulnerability in limited, targeted exploitation.
The 2025 Review Insights
Google’s Threat Intelligence Group recently reported that attackers significantly shifted how they used zero-days in 2025:
- Enterprise Focus: Nearly half (48%) of zero-days in 2025 targeted enterprise technologies (like VPNs and firewalls) rather than just consumer browsers.
- Commercial Spyware: Commercial surveillance vendors used many Chrome zero-days in late 2025 (such as CVE-2025-10585) to target specific high-profile individuals.
How to Protect Yourself?
Because these attacks happen before a fix is widely known, the best defense is speed:
- Update Immediately: When you see a “Relaunch to update” alert in Chrome or a System Update notification on your phone, apply it right away.
- Restart Regularly: Updates often don’t take effect until the application or device is restarted.
- Use Lockdown Mode: If you are at high risk for targeted attacks, mobile operating systems now offer Lockdown or Extreme security modes that disable features often exploited by zero-days.