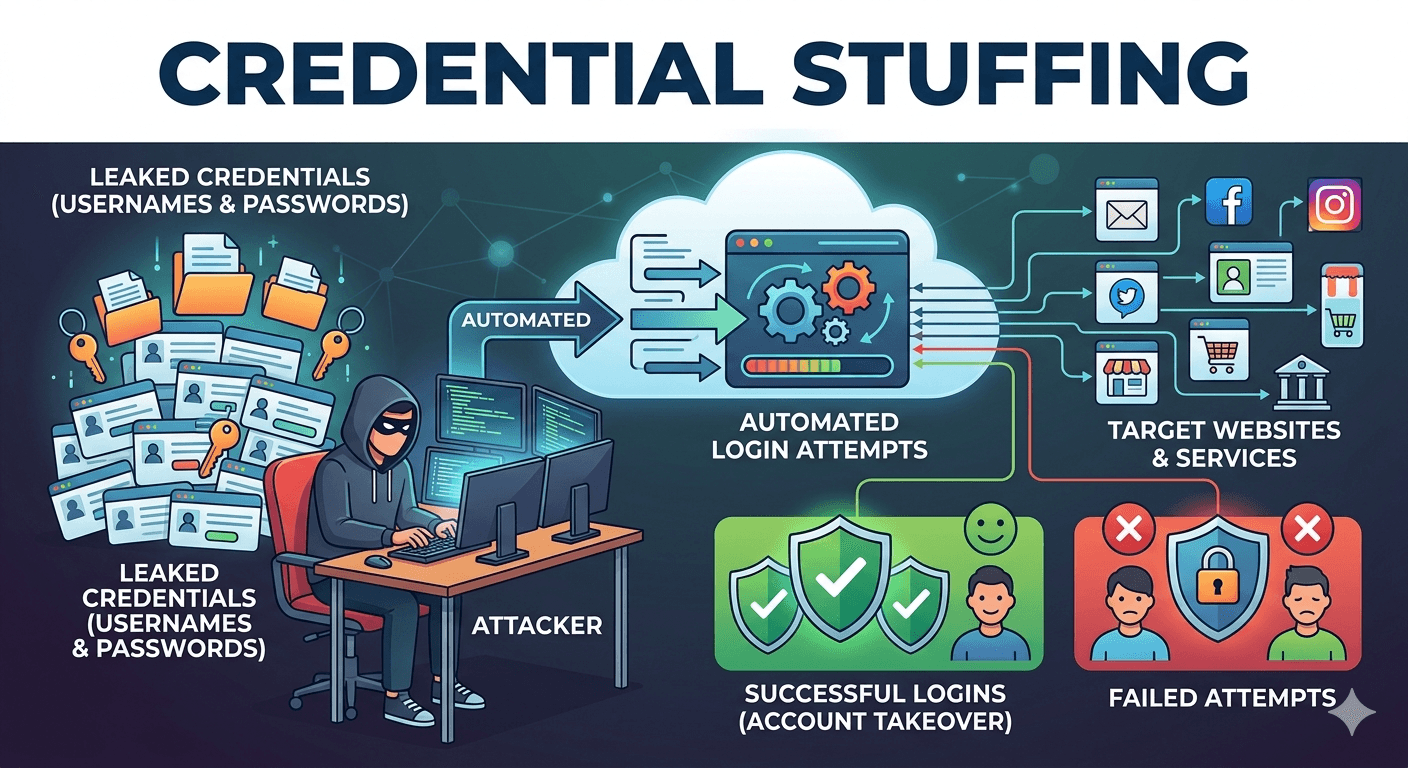
What is Credential Stuffing?
Credential stuffing is a type of cyberattack where hackers use lists of compromised user credentials typically usernames or email addresses and their matching passwords to gain unauthorized access to user accounts on other websites. This attack relies on a common habit i.e. password reuse. Because many people use the same…