Malware-as-a-Service (MaaS) is a cybercrime business model where professional developers lease or sell access to pre-built, ready-to-use malicious software and the infrastructure needed to run it.
A customer (an aspiring cybercriminal) pays a fee to a MaaS provider to use tools like stealers, botnets, or loaders. This allows individuals with very little technical skill to launch sophisticated global attacks.
How the Malware-as-a-Service (MaaS) Ecosystem Operates?
The MaaS market thrives on the dark web and encrypted channels like Telegram. It functions with professional features you would find in the legitimate software world:
- Tiered Pricing: Users can choose between monthly subscriptions, one-time lifetime licenses, or pay-per-install (PPI) models.
- Customer Support: Providers often offer 24/7 technical help desks, setup guides, and frequently asked questions for their malware.
- User Dashboards: High-end MaaS platforms provide web-based control panels where the attacker can see how many devices they’ve infected and what data has been stolen in real-time.
- Evasion Updates: To stay profitable, developers constantly update the code to bypass the latest antivirus signatures.
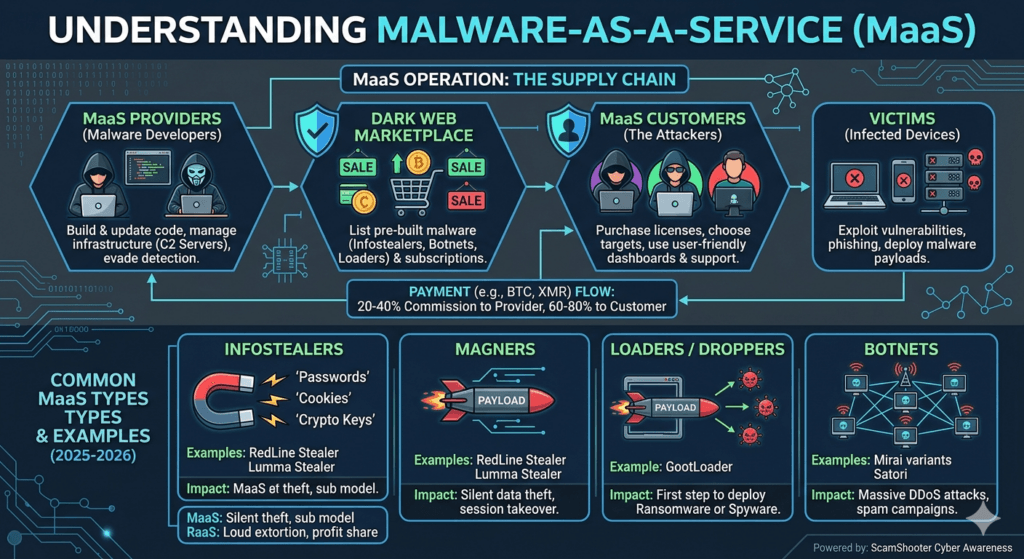
The Most Common Types of MaaS
MaaS is a broad umbrella that covers various specialized tools:
- Infostealers: Designed to sit quietly on a device and grab browser cookies, saved passwords, and crypto-wallet keys (e.g., RedLine Stealer, Lumma Stealer).
- Loaders/Droppers: Malware whose only job is to get a foot in the door and then download more dangerous software like ransomware (e.g., GootLoader).
- Botnets: Leasing thousands of zombie computers to perform massive DDoS attacks or send millions of spam emails (e.g., Mirai variants).
- Spyware: Sold specifically to monitor a victim’s screen, camera, and microphone.
Why MaaS is Booming in 2026?
The barrier to entry for cybercrime has never been lower. In 2026, we are seeing MaaS developers integrate AI-driven automation to help their customers craft more convincing phishing emails and automatically adapt the malware’s code to avoid detection by modern EDR (Endpoint Detection and Response) systems.