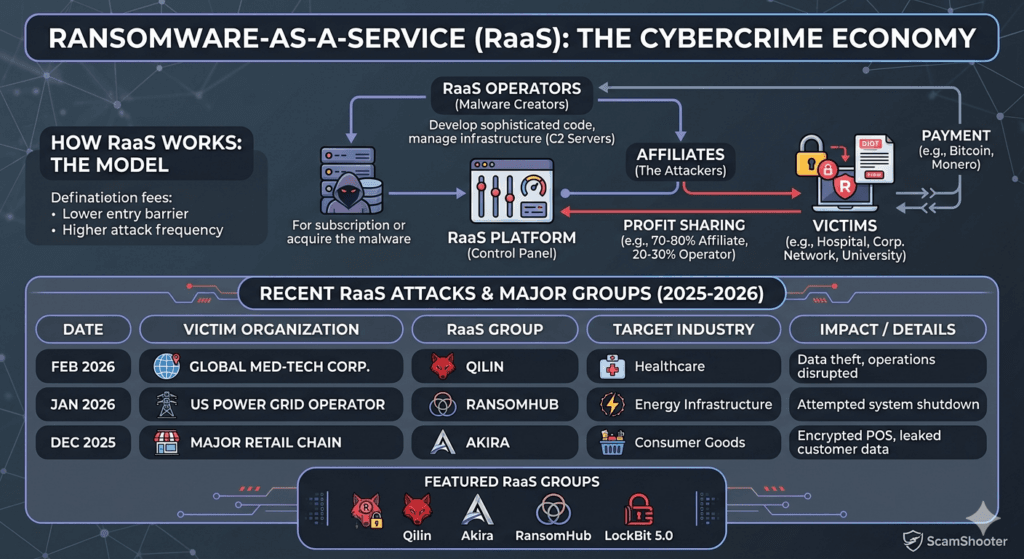
Ransomware-as-a-Service (RaaS) is a criminal business model that mirrors the legitimate Software-as-a-Service (SaaS) framework. In this ecosystem, professional malware developers (Operators) lease their ransomware code and infrastructure to other cybercriminals (Affiliates) who lack the technical expertise to build such tools themselves.
This democratization of cybercrime has led to a massive surge in attacks. Now almost anyone with a computer and a dark-web connection can now launch a sophisticated global campaign.
How Ransomware-as-a-Service (RaaS) Model Works?
The relationship is a partnership based on profit-sharing and division of labor:
- Operators: These are highly skilled developers who write the ransomware code, maintain the “Command and Control” (C2) servers, and create user-friendly dashboards for their clients. They often provide 24/7 technical support and negotiation tips.
- Affiliates: These individuals buy or lease the tools. Their job is to find targets, bypass security, and deploy the malware. They keep the lion’s share of the ransom (typically 70-80%), while the operators take a commission (20-30%).
Evolution of Extortion Tactics
Modern RaaS groups rarely just encrypt files anymore. They use a multi-layered approach to ensure payment:
- Double Extortion: They steal sensitive data before encrypting it, threatening to leak it if not paid.
- Triple Extortion: They directly contact the victim’s clients, patients, or partners to tell them their data is stolen, pressuring the victim from the outside.
- Quadruple Extortion: They launch a DDoS attack on the victim’s website while they are still struggling to recover, completely paralyzing their operations.
Prominent RaaS Groups to Watch in 2026
- Qilin (Agenda): Currently the most active group, known for scaling like a startup. They heavily recruit affiliates via dark-web banner ads and specialize in targeting manufacturing and energy sectors.
- Akira: Known for its retro cyberpunk aesthetic on its leak site. They focus on rapid encryption of Linux and virtualization (ESXi) environments.
- RansomHub: A newer group that rose to power in late 2025. They offer one of the most competitive profit-sharing models (up to 90% for affiliates), attracting many former LockBit and BlackCat members.
- LockBit 5.0: Despite several law enforcement take-downs, a new version emerged in late 2025, specifically threatening critical infrastructure like nuclear and thermal power plants.