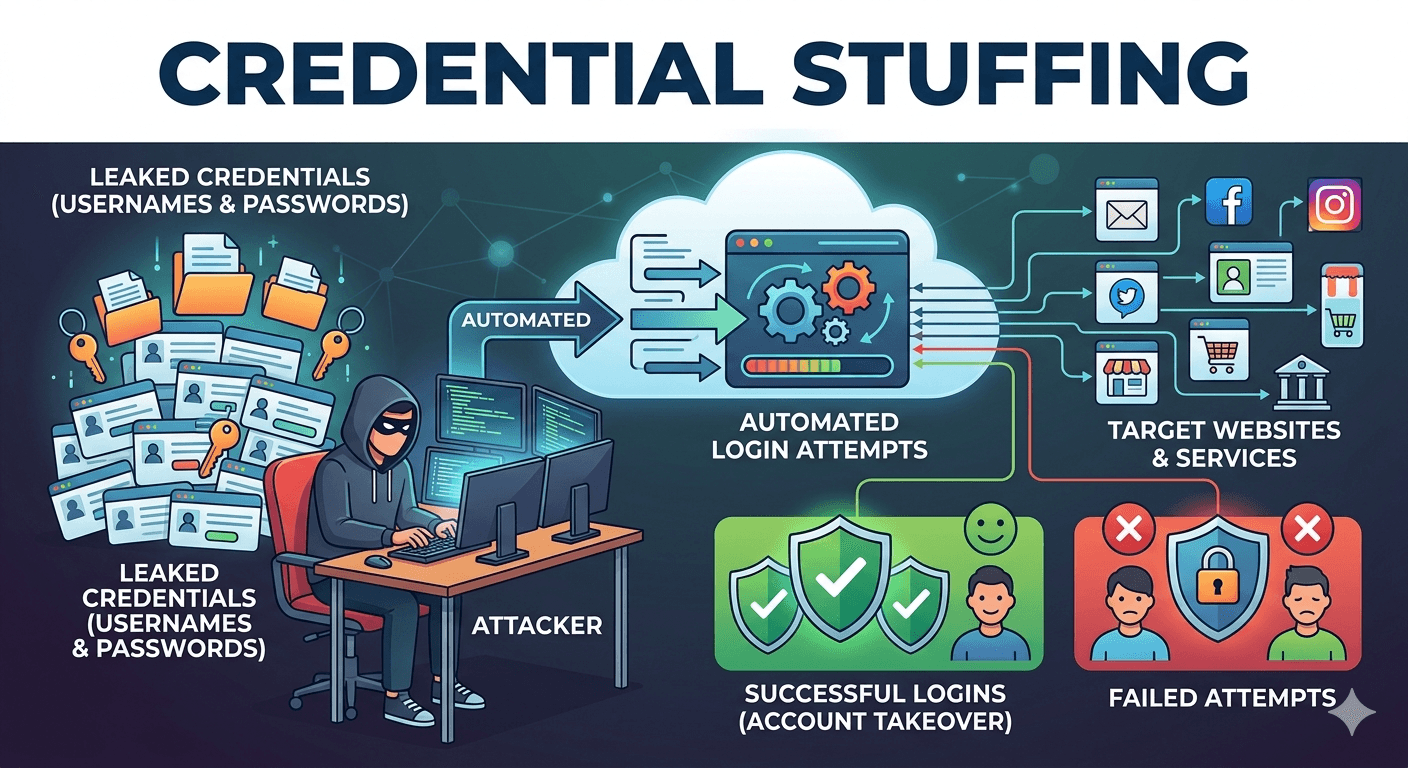
Credential stuffing is a type of cyberattack where hackers use lists of compromised user credentials typically usernames or email addresses and their matching passwords to gain unauthorized access to user accounts on other websites.
This attack relies on a common habit i.e. password reuse. Because many people use the same password across multiple platforms (like social media, email, and banking), a single data breach at one company can put all of their other accounts at risk.
How Credential Stuffing Works?
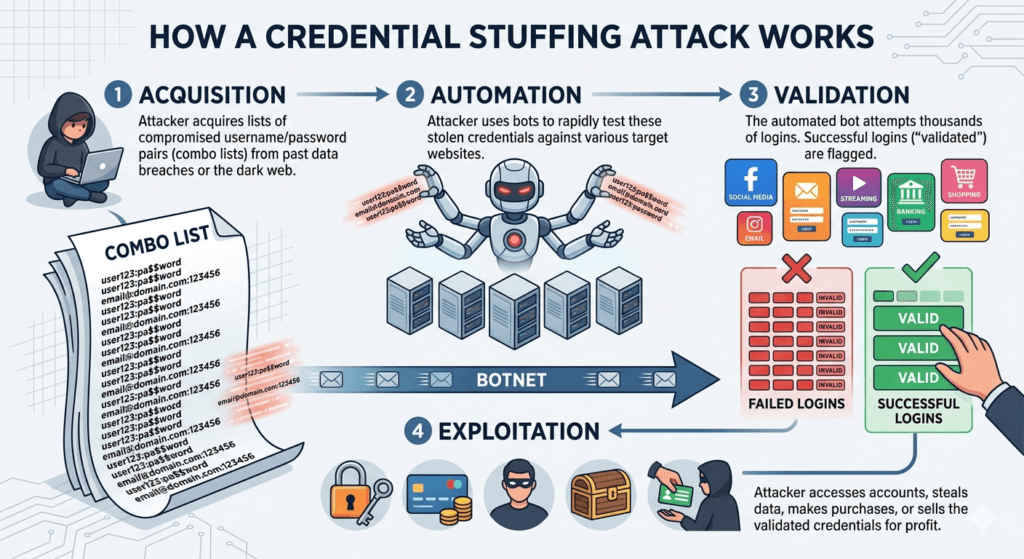
The process is highly automated and usually follows these steps:
- Acquisition: The attacker obtains a combo list (a text file containing pairs of usernames and passwords) from a previous data breach or from the dark web.
- Automation: Instead of logging in manually, the attacker uses specialized software or bots to test these credentials against various popular websites (e.g., Netflix, Amazon, or banking portals).
- Validation: The bot attempts thousands of logins per minute. When a login is successful, the software flags that account as validated.
- Exploitation: Once an attacker accesses an account, they may steal personal data, make unauthorized purchases, or sell the working credentials to other criminals.
Credential Stuffing vs. Brute Force
While they seem similar, there is a key technical difference:
- Brute Force: The attacker tries to guess a password for a specific account by trying every possible combination of characters (aaaa1, aaaa2, etc.).
- Credential Stuffing: The attacker already has a known, working password from a different site and is simply testing it to see if it works elsewhere.
How to Protect Yourself?
- Use Unique Passwords: Ensure every online account has its own distinct password. A breach on one site does not compromise the security of your other accounts.
- Enable Multi-Factor Authentication (MFA): Even if an attacker has your password, Multi-Factor Authentication requires a second key (like a code sent to your phone) to get in.
- Use a Password Manager: These tools generate and store complex, unique passwords for you so you don’t have to memorize them.
- Monitor for Breaches: Services like “Have I Been Pwned” alert you if a known data breach included your email address, signaling that it is time to change your passwords.