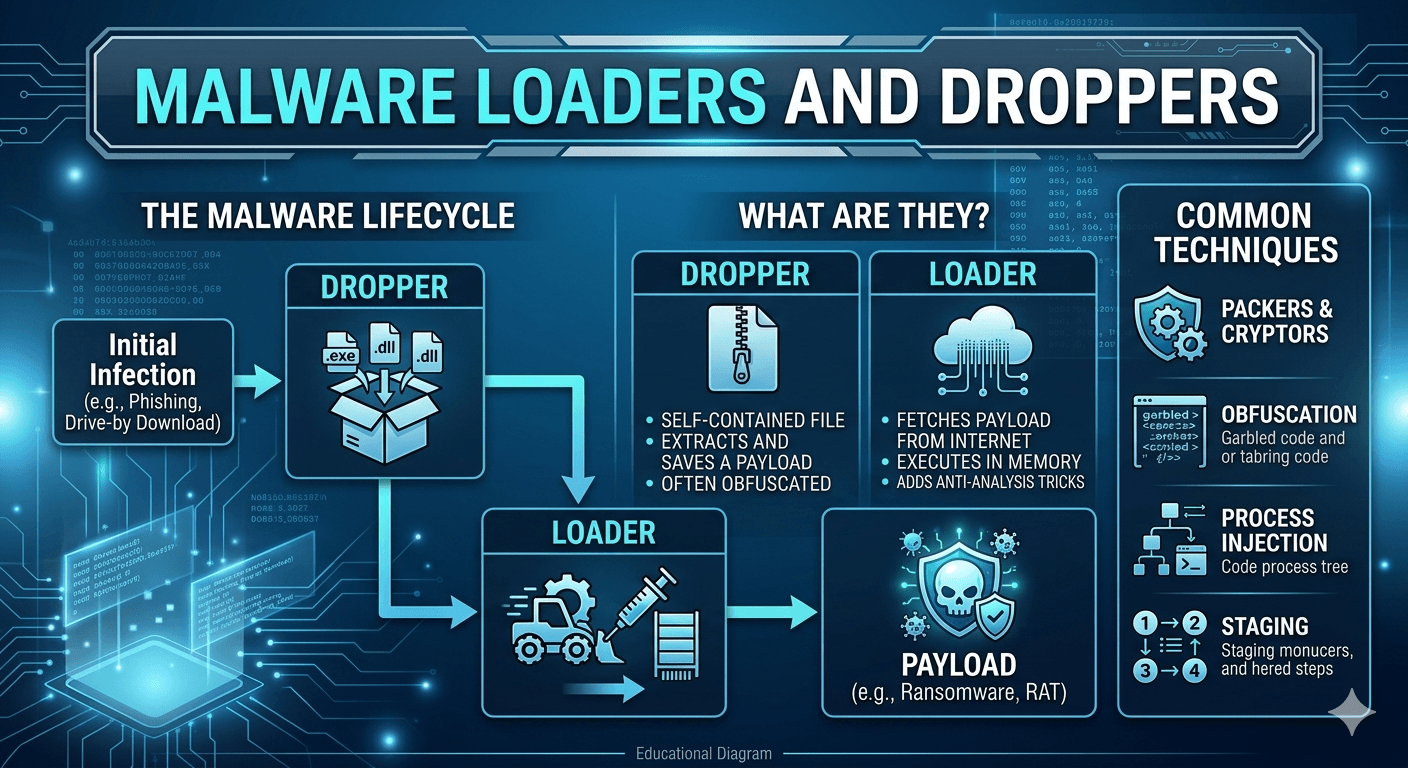
In the world of cybersecurity, Loaders and Droppers are types of helper malware designed to smuggle more dangerous threats like ransomware, spyware, or banking trojans onto a target system. While they both act as delivery mechanisms, they function in slightly different ways.
Droppers
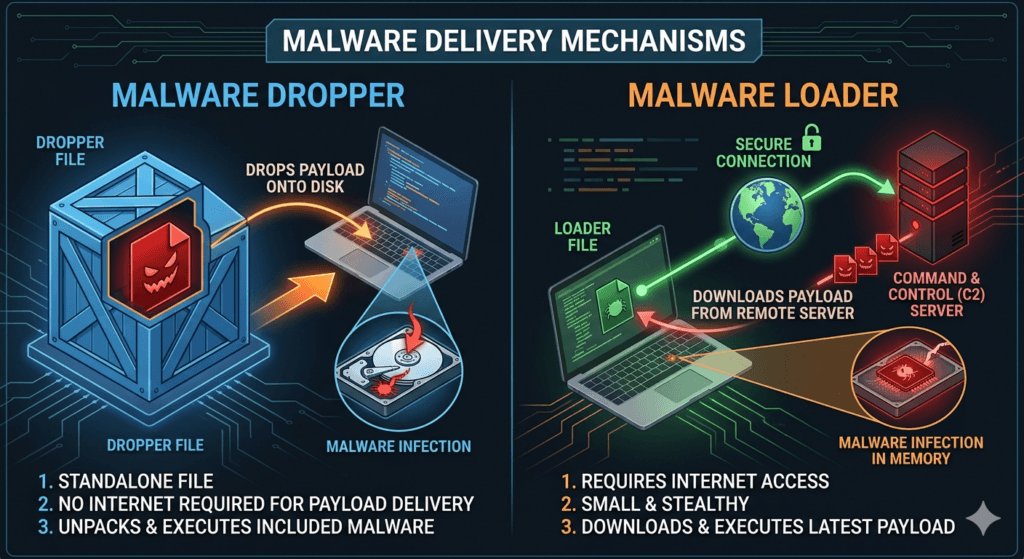
A Dropper is a standalone file that contains the primary malicious payload hidden within itself. Think of it like a Trojan Horse: the dangerous soldiers are already inside the wooden horse when it enters the city.
- How it works: The dropper executes, extracts the hidden malware onto the hard drive, and runs it.
- Key Characteristic: The dropper delivers the payload without an internet connection because its own code already embeds the malware.
- Purpose: The dropper bypasses basic file scanners by encrypting or compressing the malicious file, hiding its true nature until the system unpacks it.
Loaders
A Loader (also known as a Downloader) is a small, lightweight piece of code whose primary job is to load the final malware from a remote server controlled by the attacker.
- How it works: Once the loader infects a system, it reaches out to a Command and Control (C2) server, downloads the latest version of the actual malware, and executes it directly in the system’s memory or on the disk.
- Key Characteristic: It requires an active internet connection to pull the payload from the web.
- Purpose: Flexibility. Attackers can change the payload on their server at any time. If they want to send ransomware today and a keylogger tomorrow, they don’t have to change the loader; they just swap the file on their server.
Malware developers use both loaders and droppers to achieve obfuscation. Instead of sending a massive, easily detectable ransomware file, an attacker sends a tiny loader that looks like a harmless document or a dropper that uses sophisticated encryption to hide its contents. This allows the real malware to slip past traditional antivirus software that might be looking for specific signatures of known threats.